Entra.News #13: Dedicated to Vittorio Bertocci
Goodbye Vittorio 💔
👋 Hi folks.
I am dedicating this week’s post to one of our most beloved friends in the identity world, Vittorio Bertocci. Sadly, Vittorio lost his fight with cancer yesterday.
Nishant eloquently put in words what many of us are thinking, feeling right now in his post And just like that, he’s gone.
Here’s one of Vittorio’s final notes to all of us that he shared on LinkedIn.
Goodbye Vittorio. We will always love you 💔
In memory of Vittorio Bertocci
Super Vittorio - Anime (5 min) • YouTube
Super Vittorio in Vittorio’s own words
Vittorio has left this world today… • Matias Woloski, Auth0
Today's a pretty shitty day all over. In addition to obvious causes for consternation, we're mourning the passing of our dear friend and colleague Vittorio Luigi Bertocci • Ariel Gordon, Microsoft
Step Up from Lighthearted Joke to RFC Homage • Brian Campbell, Ping
It has finally come to pass... Today we lost a giant in the Identity world • Tarek Dawoud, Microsoft
⚡️ Microsoft
✅ Generally Available
Just-in-time access to groups and Conditional Access integration in Privileged Identity Management • Joseph Dadzie
Web sign-in for Windows • Microsoft Learn
Configure app instance property lock in your applications • Microsoft Learn
📖 Read
What’s new in Microsoft Entra • Shobhit Sahay
📺 Watch
Microsoft Entra ID Authentication Strengths Deep Dive (55 min) • Inbar Cizer Kobrinsky, Grace Picking
Deep Dive on Identity Lifecycle Workflows in Microsoft Entra ID Governance • Kristina Smith, Jef Kazimer
Microsoft Entra ID Rename Resources (35 min) • Nichole Peterson, David Parks, Mark Morowczynski
Getting Started With Microsoft Entra Verified ID (58 min) • Rohit Gulati, Karthik Muthiah, Grace Picking
From the community…
☀️ Learn
🤴 Governance
Configuring Intune RBAC just-in-time admin access with Entra ID PIM for Groups & Conditional Access • Rahul Jindal
⛑️ ID Protection
Allow On-Premise Password Change to Reset User Risk in Microsoft Entra • Daniel Bradley
🔑 Authentication
Microsoft Entra MFA Fraud Deep Dive • Christopher Brumm
Migrate MFA and SSPR Policies to Authentication Methods Policy • Sudha
Accessing On-premises Kerberos Protected Resources Using Passwordless Authentication • Andy Schneider
Move Users to Microsoft Authenticator App for MFA • Sudha
🥷 Security
Conditional Access - Common Microsoft 365 Security Mistakes Series • Ru Campbell
Easy Bulk Management of Entra ID Conditional Access Policies • Daniel Chronlund
Detect Identity-Based Supply Chain Attacks in Cloud • Sami Lamppu
🖥️ Devices
Enabling remote access for specific users on Azure AD joined devices – All about Microsoft Intune • Peter van der Woude
Convert Entra Roles to SIDs • Niklas Tinner
🤖 Workload ID & Dev
Create an Entra app with API permissions, admin consent and a secret using CLI for Microsoft 365 • Waldek Mastykarz
Create an Entra app with API permissions, admin consent and a secret using Microsoft Graph PowerShell SDK - Waldek Mastykarz
Getting Started With Microsoft Graph PowerShell For Microsoft Entra ID • Charbel Nemnom
Remove Unused Applications in Microsoft Entra ID • Sudha
How to Update User Photos with Microsoft Graph PowerShell • Daniel Bradley
Get the expiration date of application secrets and certificates in Entra • Toni Pohl
🛂 External ID
Manage Self-service Sign-up for Guests in Microsoft Entra • Shanchana
🎙️ Podcasts
So much new stuff and some other fluff • Marius Sandbu, Marius Solbakken Mellum
📺 Watch
Build a Hacking Lab for Azure Entra ID at 0 cost. (14 mins) • Sofia Marin CyberSecurity
Dynamic Groups Using Date and Times (4 mins) • John Savill's Technical Training
Privileged roles and permissions in Microsoft Entra ID (preview) (7 mins) • RioCloudSync
Got Hybrid Entra or Hybrid Azure AD users? This setting might be useful! (2 mins) • Dean Ellerby
👨🏽💻 Merill’s corner
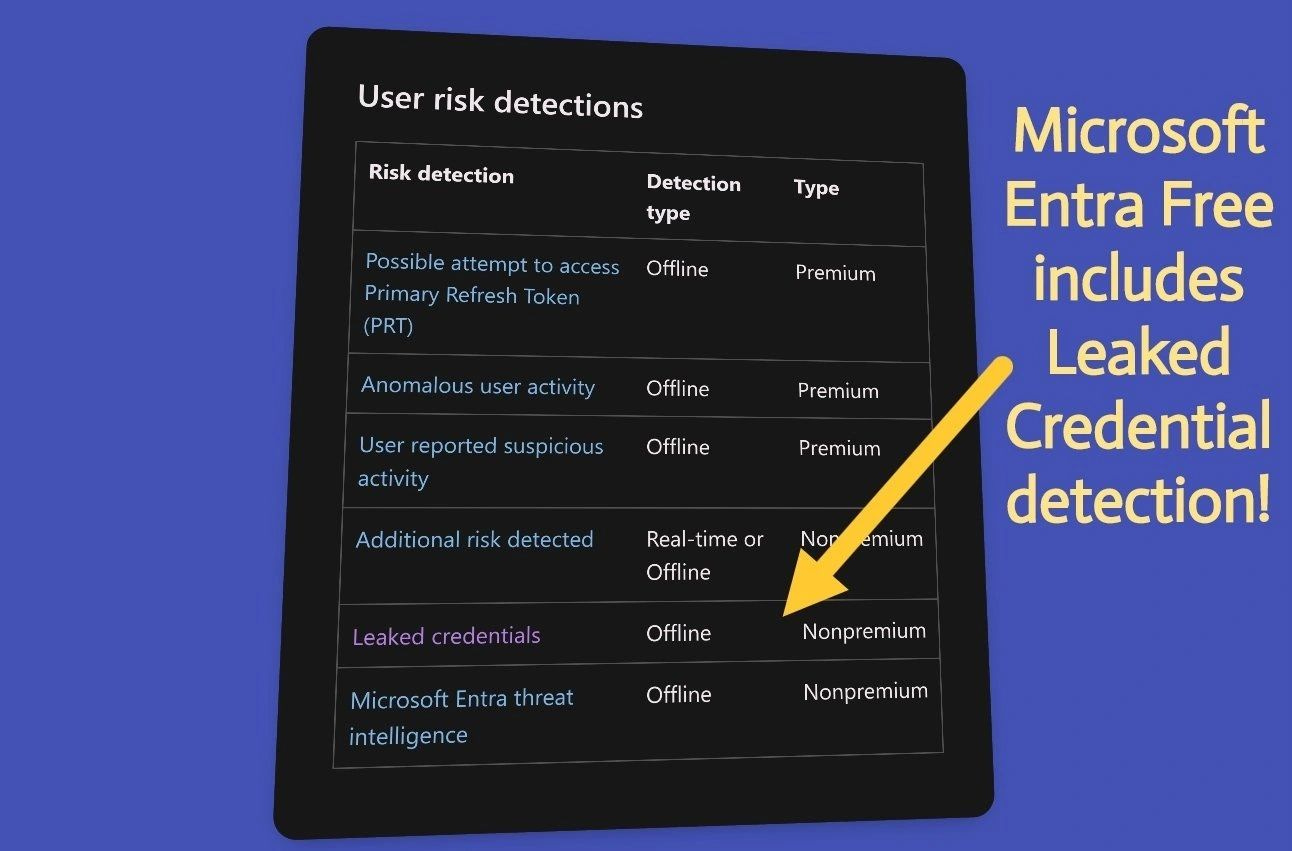
ID Protection: Leaked credential
Here's some awesome news. Microsoft Entra gives away Leaked Credential Detection for FREE in ALL editions of Microsoft Entra! 👏👏
You can use the logs or Graph API to find out when a leak is detected.
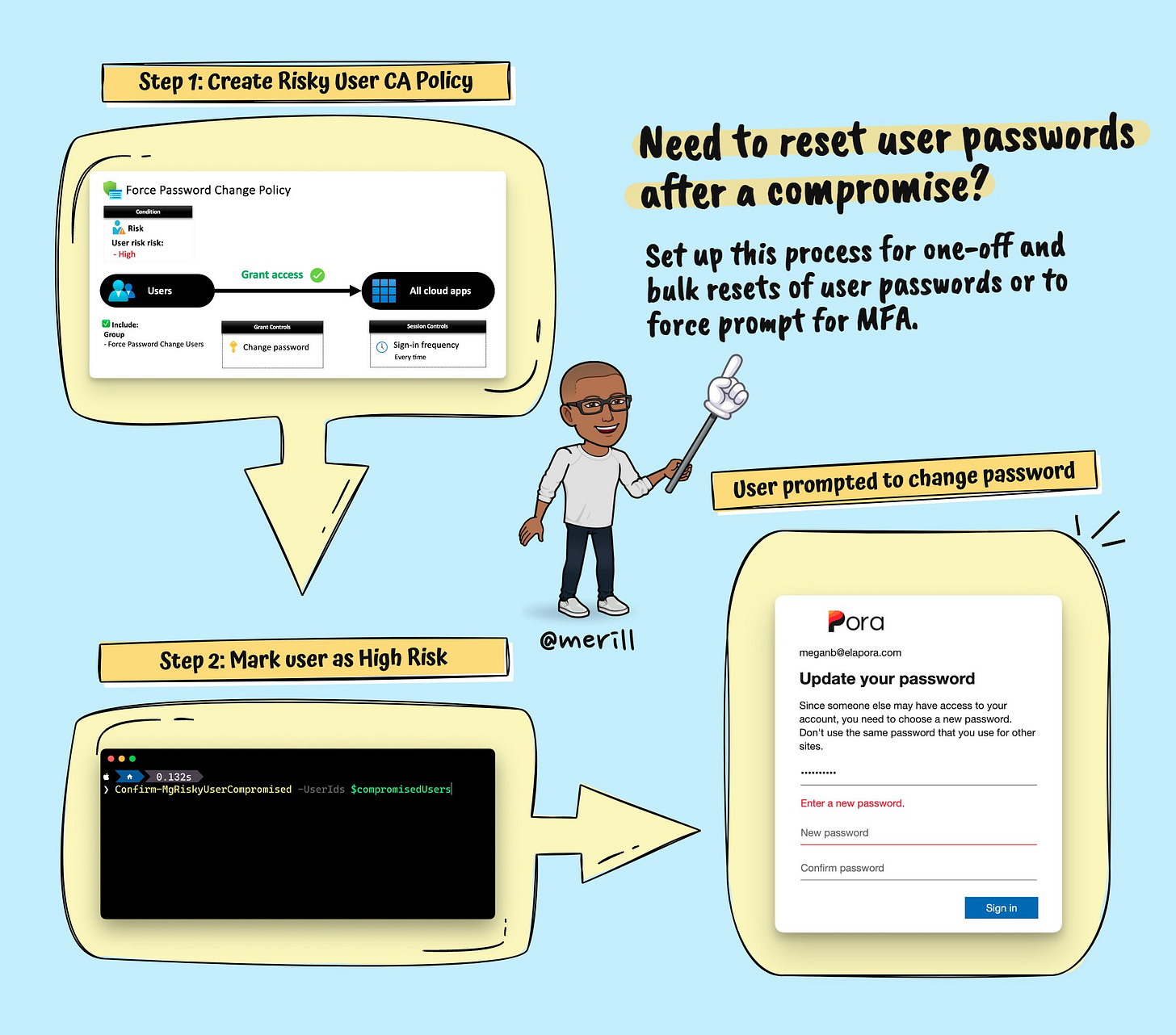
If you have P2 licenses, you can set up an automation with risk based conditional access to have the user reset their password.
You can also use your SIEM tool to trigger off a workflow.
Learn more about leaked credentials.
You can also plug in your own risk state signal with Entra ID Protection using the Graph API.
Custom Extension Properties
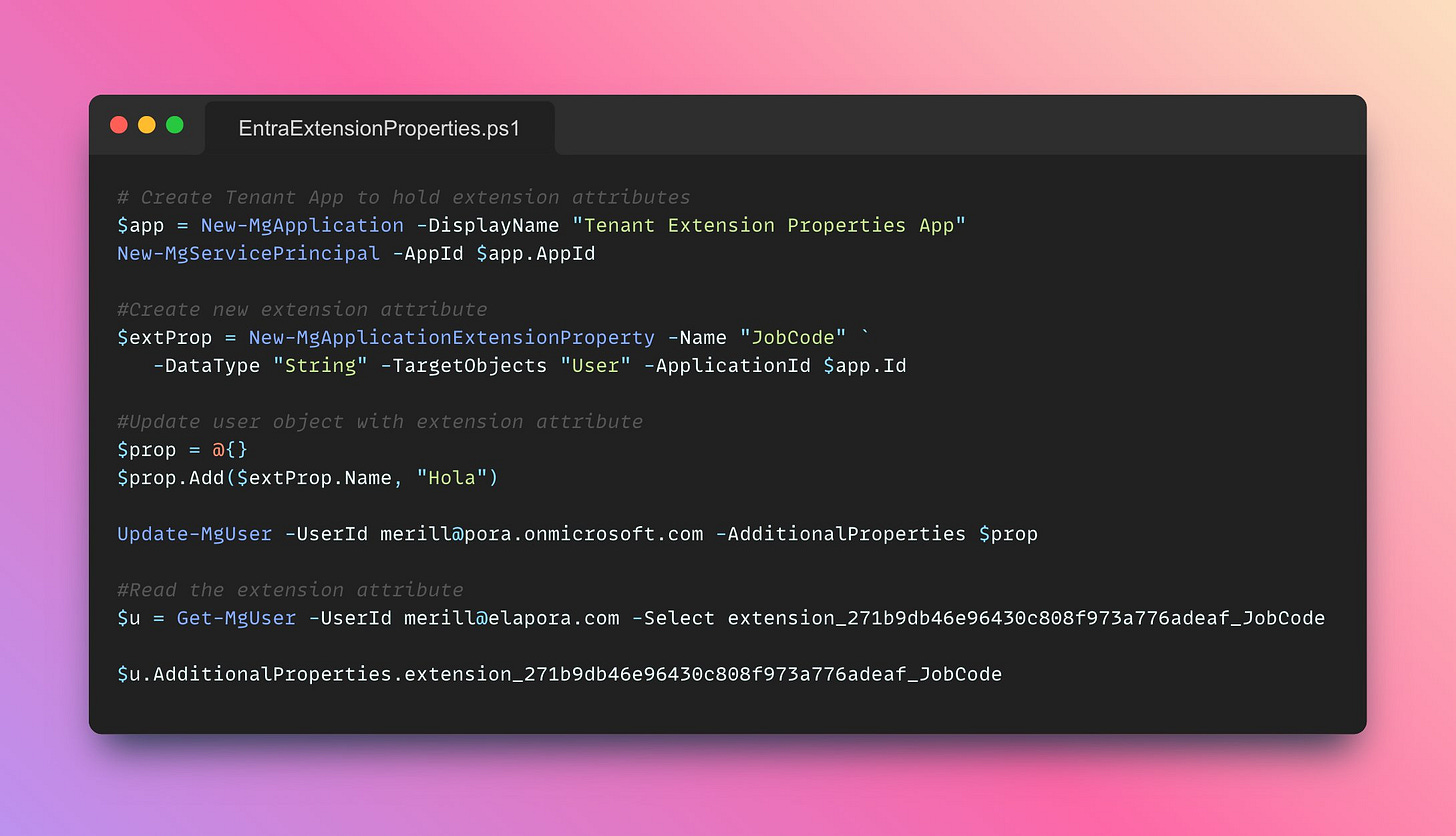
Did you know that Microsoft Entra lets you create custom properties for users, devices & other objects?
They can then be used by any app, script & even by Entra to create dynamic groups, apply conditional access policies etc.
Here's an end-to-end script showing how it's done.
Create extension attribute and update user object extension attributes · msgraph · (github.com)
Extension properties are not the only way to store data in Microsoft Entra / Microsoft 365.
You have five options to choose from based on your need.
→ Extension attributes
→ Extension properties
→ Schema extensions
→ Open extensions
→ Custom security attributes
I wrote a post comparing the different options over at Azure AD and Microsoft Graph Extensions and Attributes - merill.net
If you need your on-prem apps to be able to read the same properties you can sync them from on-prem AD to Microsoft Entra.
You can also create and update them directly using Graph API and it even works with cloud only users.
If you are building a Microsoft 365 app, this is a central place to store metadata and helps you avoid worrying about storing this externally.
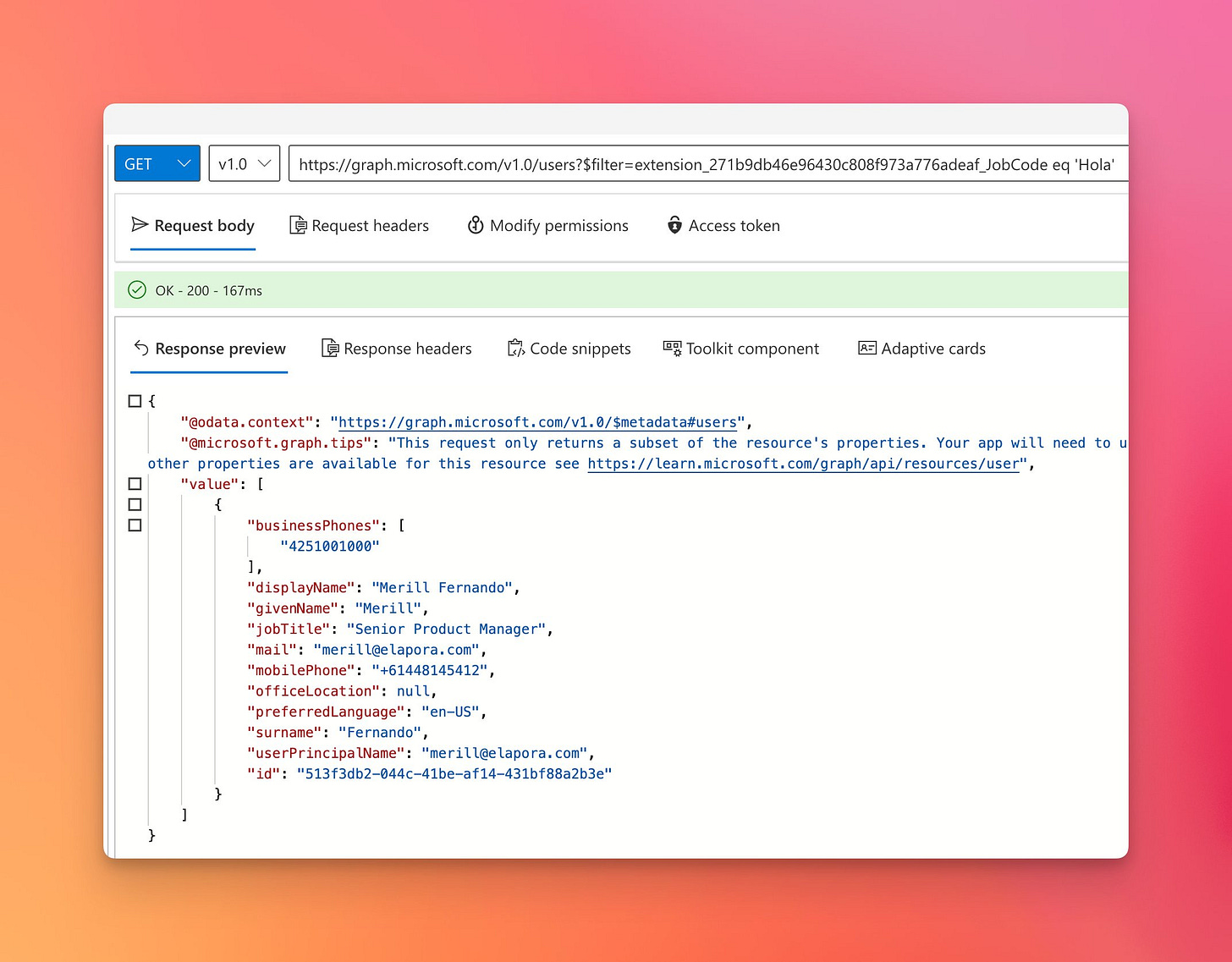
You can also use the $filter property to query Graph API for users that match the criteria.
Alternatively, you can create a dynamic group that uses this extension property.
Microsoft Digital Defence Report
🚨 The latest Microsoft Digital Defence Report came out and it is a sobering read.
In April this year a spike saw Microsoft Entra blocking 11,000 attacks per second!
Two things you can do to protect your org from these attacks.
✅ Turn on MFA (everywhere, no exclusions)
✅ Turn on risk based conditional access policies
Start planning the move to passwordless and phishing resistant sign ins like Windows Hello for Business.
Read the full report at aka.ms/MDDR
Learn about deploying conditional access policies at Building a Conditional Access policy