Entra 🆔 News #130 → This week in Microsoft Entra
Learn about detecting ConsentFix, Account Recovery and more!
👋 Hi, Merill and Joshua here with this week’s roundup of the latest news on Microsoft Entra from around the globe 🌍.
Happy New Year! 🎉
Welcome to 2026! We hope you had a restful break and are ready to tackle whatever this year throws at you. Before we jump into this week’s top posts, don’t miss our latest podcast episode with Nicolas Blank, a great conversation to help you start the year with a solid security mindset.
Now, let’s see what the community has been up to...
Enjoy!
Sponsored by:
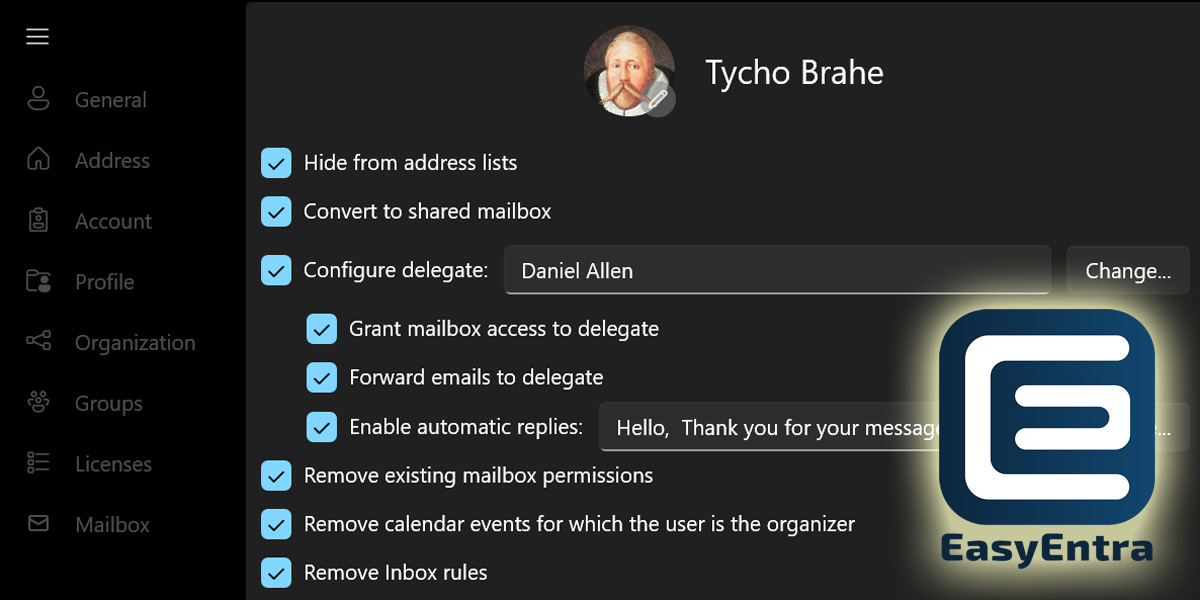
Kick Off the New Year with Automated Offboarding
A new year brings change - employees leave, roles shift, and access needs to be removed. Yet offboarding remains one of the most manual and inconsistent tasks in IT, often relying on complex PowerShell scripts and senior-level knowledge.
EasyEntra automated offboarding changes that from day one:
🚀 Eliminate the need for complex PowerShell scripting
🚀 Delegate offboarding safely to first-line support
🚀 Ensure consistent, repeatable offboarding every time
🚀 Supports both hybrid and cloud-only accounts
🚀 Free to use for tenants with fewer than 25 licensed usersSet up automated offboarding in minutes - no infrastructure changes, no steep learning curve.
“I am amazed at how much time it actually saves.”
IT System Integration Specialist, MUTH & PARTNER, Germany
From the community…
🚀 Most popular posts from last week
🥇Microsoft adds new Microsoft 365 Support Engineer role to Entra • Daniel Bradley
🥈How to Remediate Illicit Consent Grants in Microsoft 365 • Sruthy
🥉Admin Account Lifecycle Management – Part 1: Automated Provisioning with Entra ID Governance • Christian Frohn
Sponsored by:
Reveal and Remediate Entra ID Risk with AppGov Score
Worried about unmanaged or over-privileged apps lurking in your Microsoft Entra tenant? Get instant visibility with ENow AppGov Score, an app governance snapshot, including over 24 checks covering enterprise apps, app registrations, and tenant settings.
You’ll discover risky or high-privilege apps, find expiring credentials, and receive a clear, actionable Application Governance Assessment report you can share with security leadership.
Bring clarity to your identity-app landscape so you can take control and reduce your attack surface — all in about five minutes.
☀️ Learn
🌐 Private Access & Internet Access (GSA)
A second look at Microsoft Entra Private Access for Active Directory domain controllers • Chris Brumm
🔑 Authentication
Passkeys, NFC, and Microsoft Entra ID on Android: An Unexpected Breakthrough • Dr. Emin Huseynov
👥 User & Group Management
📺 Entra ID Expiration Settings Explained! (1 min) • Andy Malone
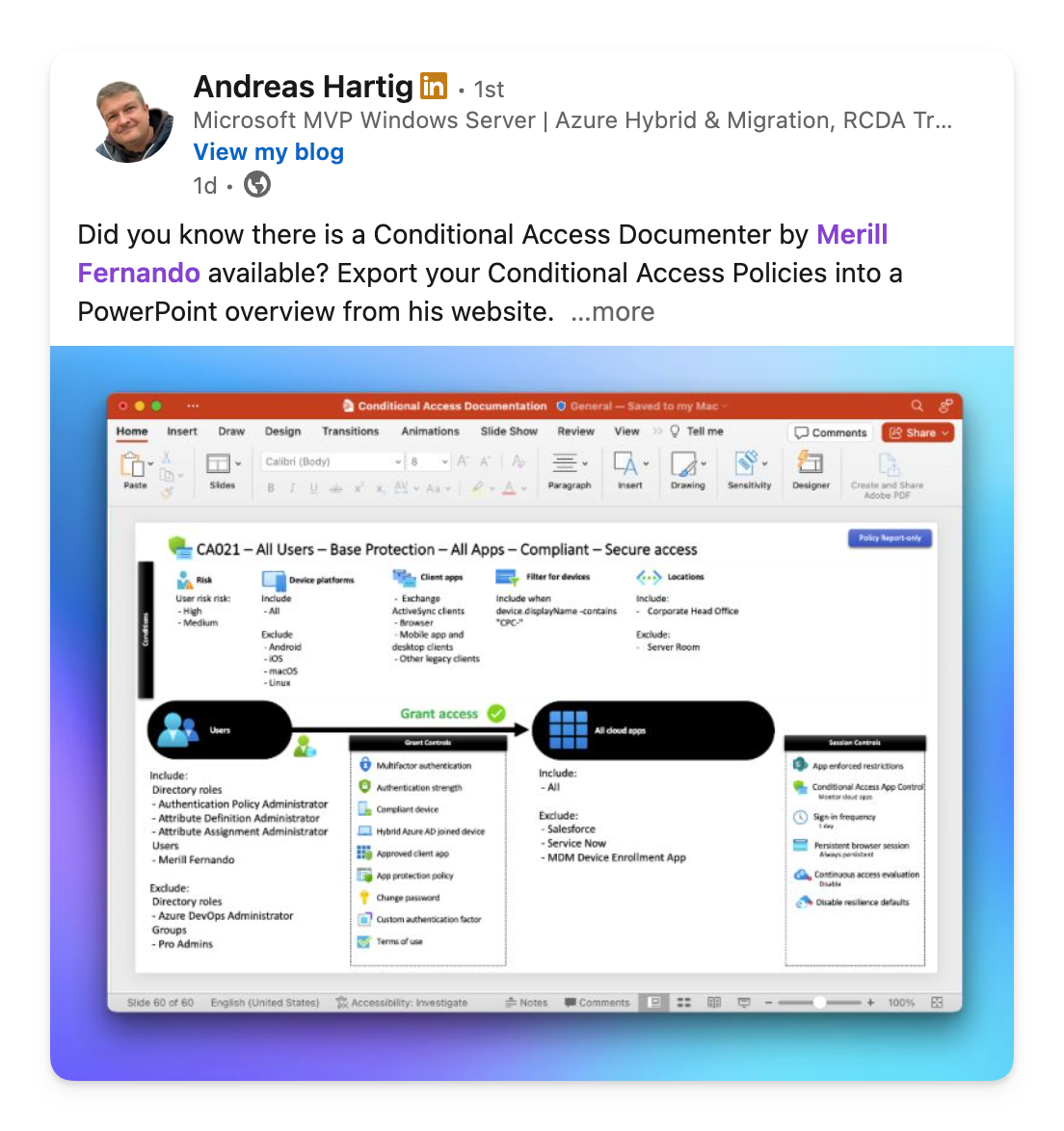
🚦 Conditional Access
How to Setup Conditional Access for Account Recovery • Daniel Bradley
🔐 Credential Management
Passkeys: A Comprehensive Guide to Modern Authentication • Sameer Bhanushali
Self-Service Account Recovery (SSAR) in Microsoft Entra ID - Getting Started Guide • Michael Mardahl
📺 Entra Account Recovery (26 min) • John Savill
🖥️ Devices
Fix Blank ‘Device ID’ and ‘Join Type’ Fields in Entra ID Sign-in Logs • Blesslin Rinu
How to Configure Personal Devices Using Entra Registered Devices • Pradeep
🥷 Security
ConsentFix: How a New OAuth Attack Bypasses Microsoft Entra Conditional Access • Fabian Bader, Christopher Brumm, Thomas Naunheim
📒 Tenant Configuration
Enterprise Certificate Pinning might hurt your Hybrid Identity security efforts this January (MC1193408) - The things that are better left unspoken • Sander Berkouwer
Want to get featured on Entra.News? → Submit your content 😎
Want us to say nice things about your company? Sponsor entra.news 🤩
Love the newsletter? Tell us 💚❤️💜
🪃 Acknowledgement of Country
Entra.News is created on Wurundjeri land and acknowledges the traditional owners of country throughout Australia, recognising their continuing connection to land, water and community. We pay our respect to them and their cultures and to elders both past and present.